Vba2Graph - 从VBA代码生成调用图,以便更轻松地分析恶意文档。
A tool for security researchers, who waste their time analyzing malicious Office macros.
Generates a VBA call graph, with potential malicious keywords highlighted.
Allows for quick analysis of malicous macros, and easy understanding of the execution flow.
✓ Pretty fast✓ Works well on most malicious macros observed in the wild
✗ Static (dynamicaly resolved calls would not be recognized)
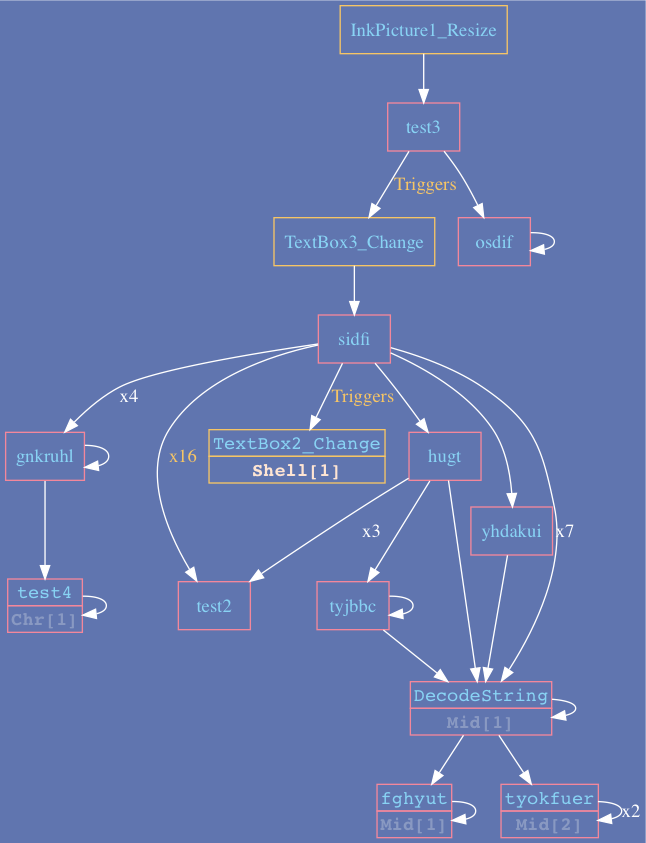
Example 1:
Trickbot downloader - utilizes object Resize event as initial trigger, followed by TextBox_Change triggers.
Example 2:
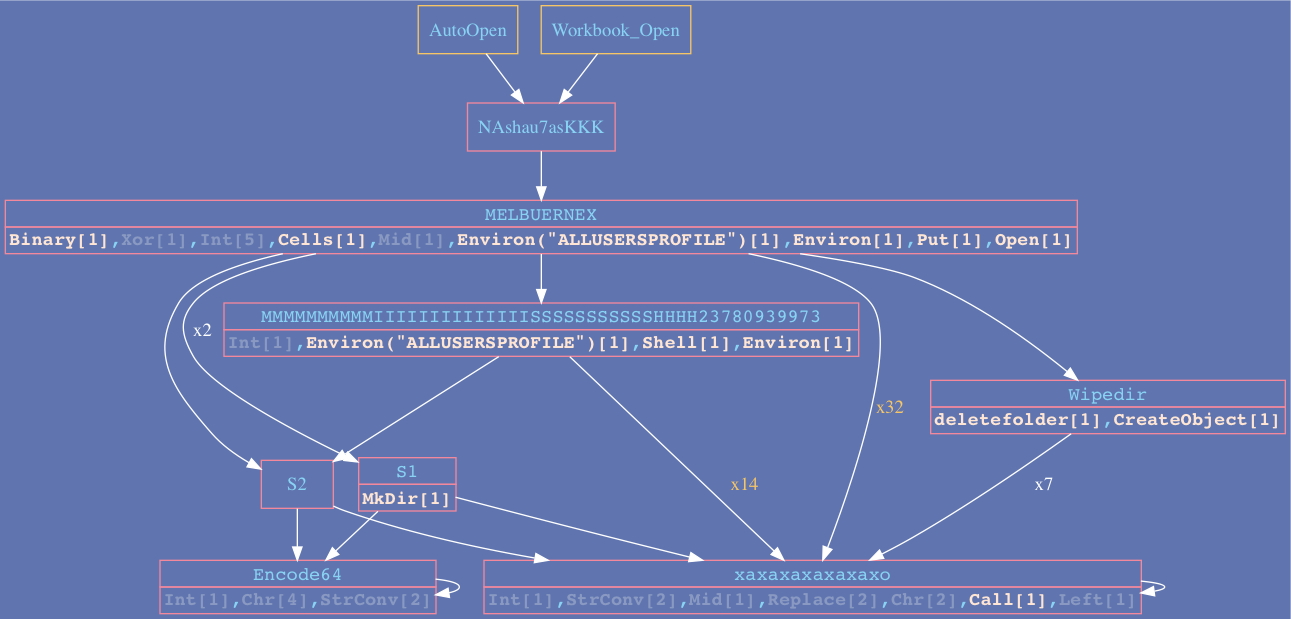
Check out the Examples folder for more cases.
https://github.com/decalage2/oletools/wiki/Install
pip3 install -r requirements.txt
Install Graphviz:
https://graphviz.gitlab.io/download/#windows
Add “dot.exe” to PATH env variable or just:
set PATH=%PATH%;C:\Program Files (x86)\Graphviz2.38\bin
brew install graphviz
sudo apt-get install graphviz
sudo pacman -S graphviz
usage: vba2graph.py [-h] [-o OUTPUT] [-c {0,1,2,3}] (-i INPUT | -f FILE)optional arguments:-h, --help show this help message and exit-o OUTPUT, --output OUTPUToutput folder (default: "output")-c {0,1,2,3}, --colors {0,1,2,3}color scheme number [0, 1, 2, 3] (default: 0 - B&W)-i INPUT, --input INPUTolevba generated file or .bas file-f FILE, --file FILE Office file with macros
Please note that a Python 2 release is availiable in the Releases section, but is no longer supported.
# Generate call graph directly from an Office file with macros [tnx @doomedraven]python3 vba2graph.py -f malicious.doc -c 2# Generate vba code using olevba then pipe it to vba2grapholevba3 malicious.doc | python3 vba2graph.py -c 1# Generate call graph from VBA codepython3 vba2graph.py -i vba_code.bas -o output_folder
You’ll get 4 folders in your output folder:
batch.sh script file is attached for running olevba and vba2graph on an input folder of malicious docs.
Deletes output dir. use with caution.
The code in this project is licensed under the EPL-2.0 License.
This project is utilizing the following third-party open-source tools and libraries.
Please note their respective licenses.